How To Minimise The Risk of Data Loss In Your Company
To reduce the potential of data loss it’s crucial to know the causes. Here we look at some common causes and ways of preventing them.

Data loss is a serious risk for businesses and companies of all sizes. Today, data is the basic fuel of business with companies relying on digital services, e-commerce and cloud storage.
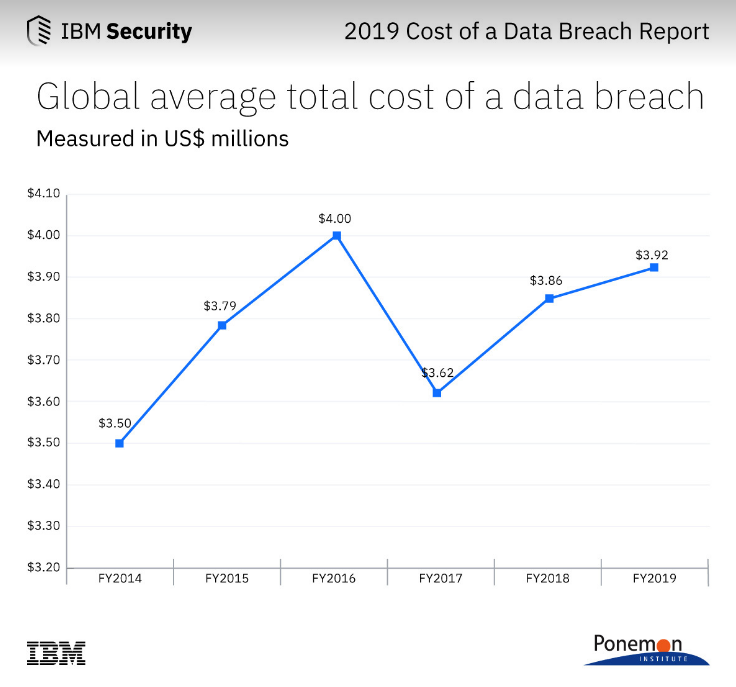
Because of this, losing data literally means losing time and money. To be more specific each record lost costs you $150 on average globally, and $155 in the UK. Data loss can happen for a number of reasons and these include accidental deletion, cybercrime, physical damage, and formatting errors.
Although in some cases, lost data can be recovered, this process requires the assistance of IT professionals. In order to help prevent data loss in your company, it’s crucial that you know what leads to it. Here are some common causes of data loss and ways of preventing them from happening.
Most Of Us Are Still Human
We all know that employees are not error-free and naturally make mistakes.
Human error is still one of the leading causes of data loss to your business. It also takes part in some other causes of data loss and they include hard drive damage, software corruption, liquid spills and hard drive formatting. The most obvious way to prevent these errors is proper training.
Your employees must understand how your company’s data processing and backup systems function. In plain words, they need to know if the documents they are working with need to be saved manually or will be backed up automatically.
Automatisation has proven itself to be the best prevention from human errors like deletion and overwriting. It simply minimises human interaction with sensitive data.
Optimised workflow is also a great way of prevention because it basically leaves little room for human error while saving workers time.
Pesky Viruses
Next to hacking, viruses and malware are the number one threat to companies and their data.
They are able to delete or steal precious data or slow down business operations which in the end destroys company functionality.
The most common way to get a virus is through an email based attack or phishing, where employees are tempted and click on a corrupted link. Previously we talked about email security protocols, so make sure to read up on that.
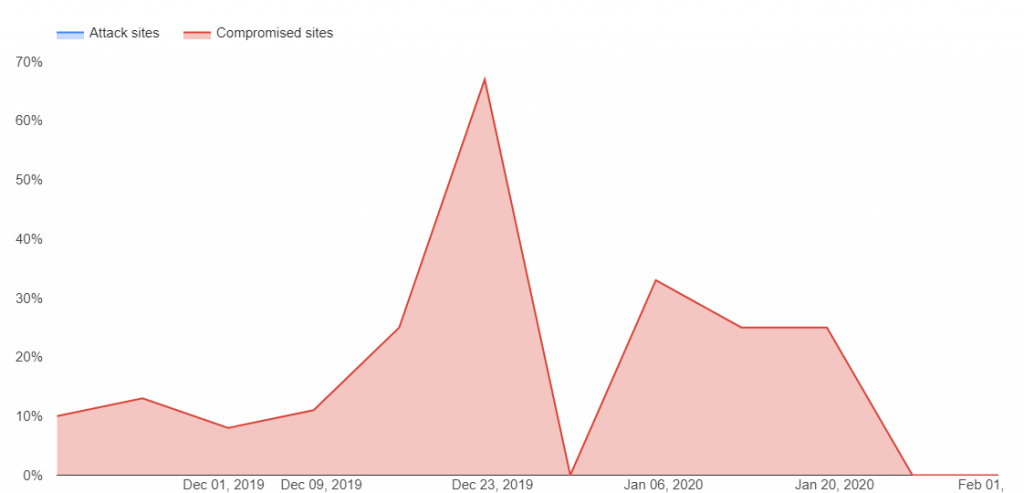
Google reported a huge decrease of malware websites in 2019. This is nothing surprising as the natural state of malware websites and Google is to always play the game of cat and mouse, that’s why this chart always has spikes.
In order to guard your computers against viruses and malware it’s vital to install appropriate anti-virus software. Always keep them updated and run regular scans, removing viruses and malware before they can do any serious damage.
Also make regular system backups just in case a malicious programme somehow enters your system.
With the BYOD trend being more prevalent in recent years, it’s advised that you limit the use of portable devices in your company. Research done by Symantec shows that 21% of companies experience data leak via BYOD.
With so many devices connected to your system, USB ports could be the main culprits of data leaks.
A simple USB lamp can be modified so that it captures every keystroke, and transmit it to another computer via Bluetooth. Make sure that your employees don’t use devices that they don’t fully trust.
Hardware Failure
Data is often lost due to physical data storage unit malfunction and failure. Apart from external issues like magnetic fields and overheating, hard-drive failure can also be attributed to internal issues like software corruption.
Over time, just like with any machine a hard drive will stop working so it’s vital that you recognise the signs of imminent failure. Some of them are frequent crashes, slow processing speeds, clicking or grinding noises and overheating.
Today, traditional HDDs are slowly being replaced by SSD (solid-state drives). The big advantage of an SSD is that it doesn’t have any movable parts, and are less prone to malfunction or crash. Some downsides of SSDs were its price and their ‘’writing’’ limit. With recent advances, the writing limit was exponentially increased, and even the cheapest drives are able to deliver 2.5 times more writing space than promised on the label.
When comparing space provided and the price, HDD is still winning, but with more and more businesses going to the cloud this fact is becoming extraneous.
Overall, it is crucial that you take preventive measures in protecting your computer data regardless of the type of hard-drive it has. According to Disk Drill Data Recovery for Mac, there are many different ways to recover data from damaged disks, devices and even websites. However, if you have problems with your hard drive, there are cases when even professionals can not fully recover the data, all depends on the degree of damage. Components of the most modern Macbooks have a hard drive that eventually has the potential to break.
Going Back To The Dark Ages
When power outages occur, systems shut down without warning and grind your business operations to a halt. Although this doesn’t happen very often, unpredicted shutdowns not only cause loss of data but the corruption of your existing files.
Regardless of many programmes having autosave features, most operating systems require complex shutdown procedures, which if not followed can even cause damage to your hard drives. In order to minimise the chance of power failure harming your data, the best way to go is to make regular and automatic system backups.
Another solution for this issue is cloud technology. It allows you to store data on the internet instead of using the storage space on your computer. Your information is kept in virtual servers which connect back at datacentres. These centres have the infrastructure to protect your data much better than your average on-premises IT team.
Hackers And Insiders
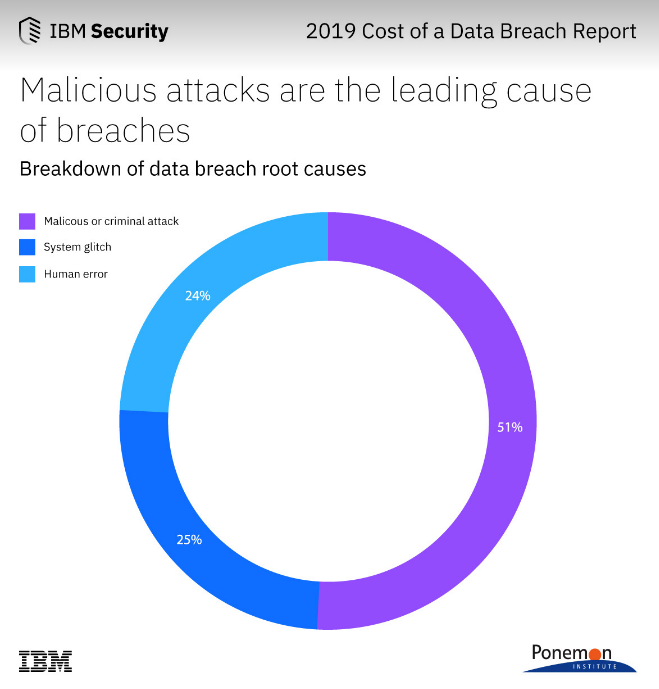
In 2019 51% of data breaches included hacking and 28% involved malware. For your company not to be included in this statistic, serious cyber-security measures must be put in place.
If hackers possess sufficient access to your system they can cause serious damage to your data and can even damage entire network processes. To keep hackers out of your system always use servers with good security, have adequate firewalls and, as said before, use passwords that aren’t easy to hack.
Apart from hackers, data is sometimes stolen by insiders. This happened to a Canadian bank recently when one of its employees shared customer information with a third party. Information of 2.7 million people and 173,000 companies were affected. Of course, the employee was instantly fired, but that couldn’t mend the massive damage in customer trust and brand image.
To avoid this consider implementing different levels of permission for employees because it will make it harder for insiders to access your company’s high-level data.
Increase Password Strength
With the amount of sensitive data on your hands, it’s mandatory to create a password-protected environment. In 2019 Facebook admitted that since 2012 it didn’t properly secure passwords of over 600 million users. The same study shows that 38% of users have passwords that never expire, this could be a huge flaw in your security armour.
The first step in password protection is to always use two-factor authentication.
With this system, employees will receive a message on their smartphones through which they will acquire a second set of codes in order to access an account. In plain words, two-factor authentication helps confirm the identity of a person trying to access sensitive data.
Here are a few more do’s and don’ts when it comes to password generation:
Do's
Don’ts
Really Simple Systems is now Spotler CRM
The same great technology, a CRM platform that is focused on the needs of B2B marketers, provided by the same great team, at a great price!