Don’t Get Caught by Spear Phishing
Spear Phishing, the term given to fraud directed at specific companies by email to extract payment, is on the rise. Make sure you don’t get caught.
Increased Incidences of Spear Phishing
Spear Phishing is on the rise, but you can avoid capture by making sure your team is not taking the bait!
Spear Phishing is when a fraudster tailors an email, asking for funds to be transferred, specifically targeting an organisation. We’ve certainly noticed an increase though, fortunately, all have been identified without any money changing hands.
Spear Phishing Example
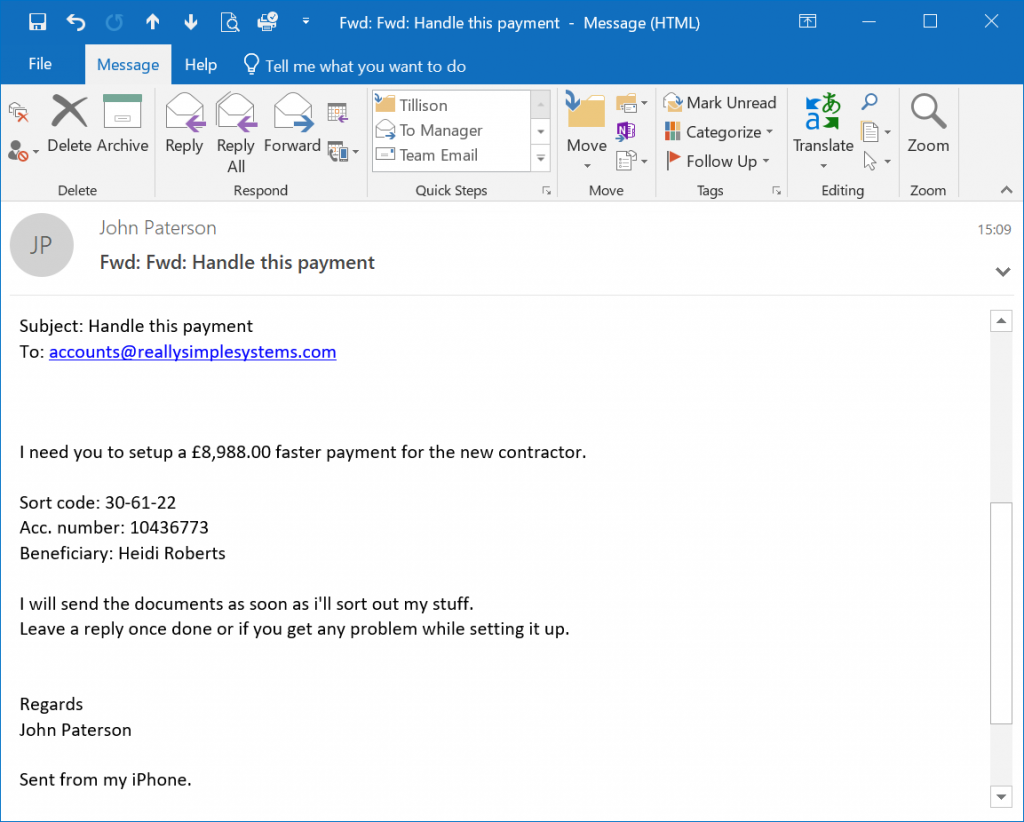
The example below shows an email we received recently, professing to come from our CEO, John Paterson. On this occasion, the email used is quite similar to John’s address, but we have also had ones appearing to be from his actual address.
The emails are often sent to an individual within the organisation or to a generic email address like finance@ or accounts@, asking for an urgent bank transfer. More often that not this has occurred when our CEO is on holiday!
Alarm bells!
In this case, the giveaways were that the reply email address was close, but not correct, he doesn’t use an iPhone, and the recipient knew that our CEO was never lazy enough not to capitalise the “I” in “I’ll”!
These attacks are becoming more frequent and are ever more sophisticated, targeting everyone from small companies to the largest. Facebook and Google were hit for $100m between 2013 and 2015.
Make Sure You Don’t Get Caught
Businesses should tell all staff who have access to bank payments to be aware of such attempts, and how to check if they are legitimate:
Really Simple Systems is now Spotler CRM
The same great technology, a CRM platform that is focused on the needs of B2B marketers, provided by the same great team, at a great price!